Enterprise Mobility Management
A set of technology, processes, and policies to secure and manage the use of corporate and employee owned mobile devices within an organization.
Boost Productivity with Digitalization
Retailers, transportation and logistics, healthcare, manufacturers and warehouses, field services are mobilizing operational processes using mobile devices and managing the bulk device with the ease of Enterprise Mobility Management solutions.
Streamline Workforce Mobility & Mitigate Risk
Enterprise Mobility Management able to handle your massive burden in managing remotely extensive and expanding use of mobile device that across multiple operating system. EMM has also evolved to cover more type of devices beyond mobile, laptop, tablet, and also wearable devices.
Mobile device security protects your data from threats that lead to data breaches, unauthorised access to sensitive data, and even data loss as a result of user error or a stolen or misplaced device. It is possible to protect employees and organization with a managed mobile device security contingency plan.
Applicable Industries
License Sold
Satisfied Client
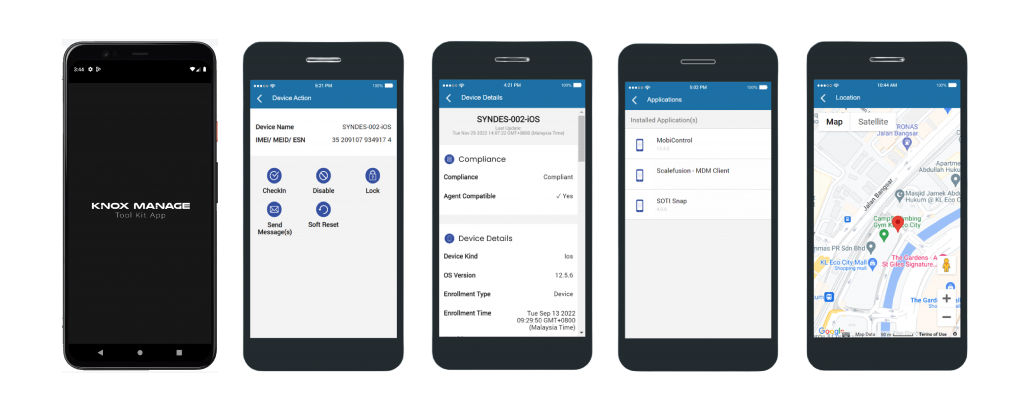
EMM Tool Kit | Handy Manage Anywhere
Enterprise Mobility Solutions is now even easier with EMM Tool Kit. Manage and monitor your mobile devices at our handy app. Keep track the status and analytics wherever and whenever you are.
Other Amazing Features
Manage iOS, Android and Windows Devices

Zero Touch Installations
Zero touch installations to remove deployment nightmares. Single dashboard enrollment, able to see all devices. Successful device being enrolled.
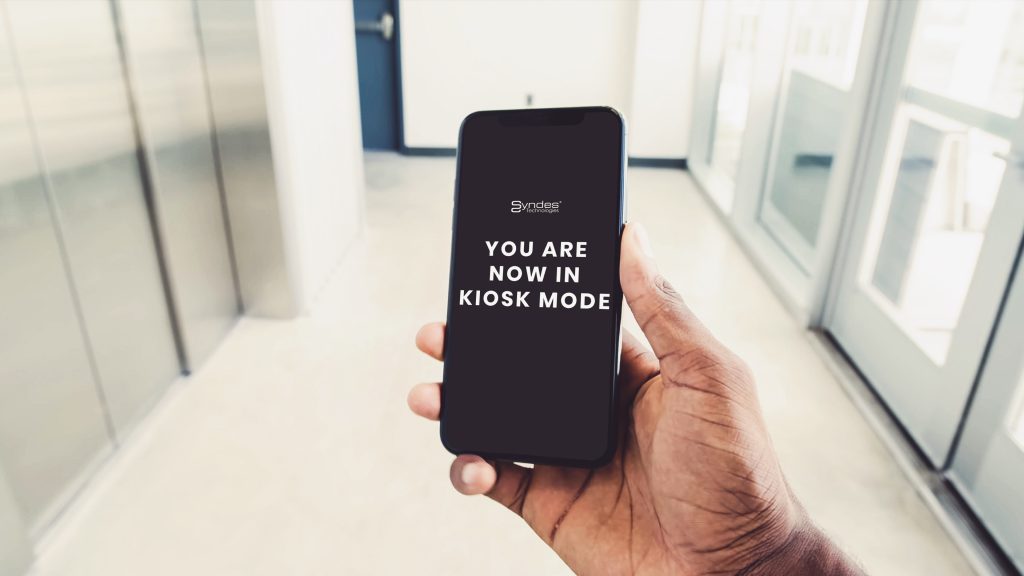
Device Lockdown
Lock your devices to kiosk mode & remote control at business will. Kiosk mode simple illustration
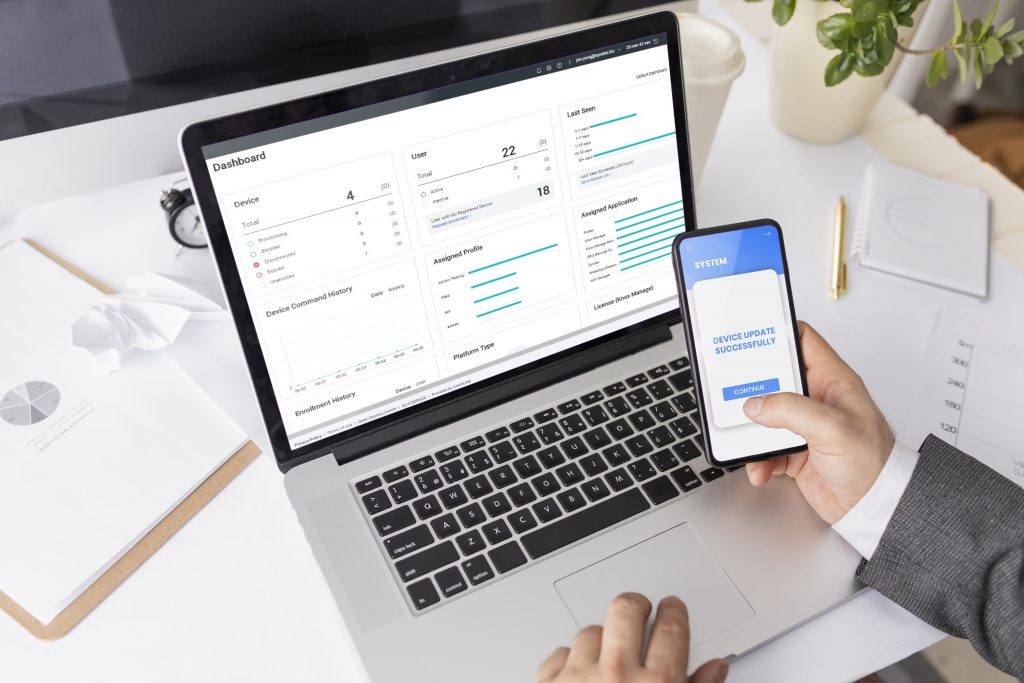
Control Over-The-Air
Reboot devices remotely, updating devices, notification, application, functions or policies instantly.

Custom-Built Device
You brand as your persona, customization of persona. Boot up customization

Power Location-Based Tracking Experience
Locate, track and enforce restriction parameter or lockdown on dynamics groups to have all the devices in violation automatically restricted.

Fortify Both Corporate & Personal Data
Secure corporate data by remotely locking or wiping stolen devices. Delete apps and settings at all times.






